Monetization SDKs use their peers’ network traffic – how safe is that? In this article, we’ll explain what “using network traffic” actually means in the context of peer-to-business networks, who uses it and why, and what real-world use cases it supports. We’ll also clarify what this process does not involve, and how strict security, compliance, and verification measures ensure that user participation remains safe, transparent, and fully under control.
What Does “Using Network Traffic” Actually Mean?
At a basic level, network traffic refers to the data sent and received when a device connects to the internet. Every time a website is opened, a search is performed, or a page is loaded, requests are sent and responses are received. This is a normal part of how the internet works.
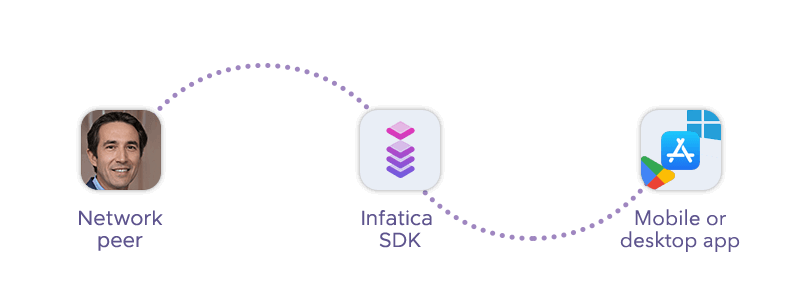
In a peer-to-business (P2B) network like Infatica’s, this traffic is used to route requests from businesses through real user IP addresses. These requests are made to access publicly available websites – similar to how any user would browse the internet. The goal is not to interact with personal data, but to retrieve publicly accessible information in a reliable and location-accurate way.
For example, a company might want to check how a product price appears in different countries or how search results vary by region. To do this accurately, they need to view websites as real users in those locations would. This is where network traffic comes in: it enables those requests to be routed through real connections, ensuring accurate and unbiased results.
Who Uses This Traffic – and Why?
Understanding who uses network traffic – and for what purposes – is key to building trust in the model. In the case of Infatica’s peer-to-business network, access is limited to verified companies that rely on publicly available web data to operate effectively.
B2B Companies Only
The network is not open to individuals or unknown actors. All traffic buyers are businesses, typically operating in areas such as e-commerce, digital marketing, SEO, market research, and cybersecurity.
Before gaining access, each company goes through a verification process to confirm its identity and intended use cases. This ensures that participation in the network is restricted to legitimate, accountable organizations.
Why Businesses Need Network Traffic
Companies use network traffic to access publicly available information on the web in a way that reflects real user experiences. This is especially important because many websites display different content depending on location, device, or browsing context.
Without access to real-world connections, businesses may see incomplete, biased, or blocked data. Reliable traffic allows them to operate with greater accuracy and consistency.
Accurate, Location-Based Data
Many use cases depend on seeing how content appears in different regions. For example, product prices, search results, and even available inventory can vary significantly from one country to another.
Real-World Use Cases of Network Traffic
To better understand how network traffic is used in practice, it helps to look at the real-world scenarios it supports. In all cases, the goal is the same: to access publicly available web data in a way that reflects how real users experience the internet.
Price Aggregation Platforms
Price aggregation platforms rely on accurate, location-specific data to compare product prices across different retailers and regions. Since prices can vary depending on geography, accessing websites through real user connections allows these platforms to display the most relevant and up-to-date information.
This ultimately benefits end users, who can compare offers more effectively and make better purchasing decisions.
Search Engine Optimization (SEO)
SEO professionals need to understand how search engine results appear in different locations. Rankings, featured snippets, and even entire result pages can change based on geography and user context.
By using real network traffic, companies can view search engine results as actual users would see them, helping them track performance, optimize content, and improve visibility in specific markets.
Brand Protection
Brands use web data to monitor how their products and assets are represented online. This includes identifying counterfeit goods, detecting unauthorized sellers, and ensuring pricing policies are followed.
Access to reliable network traffic makes it possible to scan marketplaces and websites from different regions, helping companies respond quickly to potential violations and protect their reputation.
Market Research and Analytics
Market research often depends on large volumes of publicly available data. Companies analyze competitor websites, track trends, and monitor changes in product offerings or pricing strategies.
Using distributed network traffic allows researchers to collect this data at scale while maintaining accuracy across different regions and platforms.
Academic and Public Research
Beyond commercial use, network traffic also supports academic and institutional research. Universities and research organizations use publicly available web data to study topics such as economics, social trends, and digital behavior.
Reliable access to web content ensures that research is based on comprehensive and unbiased datasets.
What Network Traffic Is NOT Used For
When discussing network traffic, it’s just as important to clarify what doesn’t happen as what does. Many concerns come from assumptions about data access or device control – so setting clear boundaries helps eliminate uncertainty.
First and foremost, network traffic in this context is not used to access any personal data. There is no visibility into files, photos, messages, emails, or any other private content stored on a user’s device. The system does not interact with personal folders or extract information of any kind.
It also does not involve tracking individual user behavior. The network isn’t designed to monitor what users browse, which apps they use, or how they interact with their devices. Participation does not translate into surveillance.
Equally important, there is no access to personal accounts. The traffic is not used to log into services, interact with user profiles, or perform actions on behalf of a user. It simply routes requests to publicly accessible websites – nothing more.
The network is also not used for illegal, unethical, or harmful activities. Access is restricted to verified businesses with clearly defined use cases, and all activity is monitored to ensure compliance with strict guidelines. Any misuse is actively prevented and addressed.
Finally, participation does not interfere with normal device usage. The SDK is lightweight and designed to run without disrupting performance, draining resources, or affecting the user experience.
Security Measures Protecting Users
Any system that involves network participation must be built with security at its core. In the case of Infatica’s peer-to-business network, multiple layers of protection are designed to ensure that participation remains safe, controlled, and fully compliant.
Built-In Threat Protection
To safeguard users from malicious activity, Infatica partners with Bitdefender, a globally recognized cybersecurity provider. This adds an additional layer of protection against threats such as fraudulent or unsafe websites, phishing attempts, and other forms of harmful traffic.
All requests routed through the network are filtered and evaluated to minimize risk and prevent exposure to potentially dangerous destinations.
No Personal Data Collection
User privacy is a foundational principle of the system. The SDK does not collect, store, or process personal data. There is no access to files, browsing history, or sensitive information on the user’s device.
This ensures that participation in the network does not compromise privacy or create additional data exposure risks.
Verified and Monitored Network Usage
Every company that accesses the network is carefully vetted before being granted access. This verification process helps ensure that only legitimate, accountable businesses can use the infrastructure.
Beyond initial verification, all activity is continuously monitored. This allows Infatica to detect unusual patterns, enforce compliance, and prevent misuse in real time.
Compliance with International Standards
Infatica adheres to strict global standards for security, privacy, and operational reliability, including ISO/IEC 27001, ISO/IEC 27701, ISO 22301, and ISO/IEC 20000-1.
The network is also fully GDPR-compliant, meaning user rights and data protection principles are upheld at every level.
User Consent and Transparency
Security is not just about technology – it also involves clear communication and user control. Participation in the network is always based on explicit user consent, and developers are required to clearly explain how the system works.
Users remain informed and in control of their involvement, which reinforces trust and ensures that participation is both voluntary and transparent.
How Infatica SDK Fits Into This Model
Infatica SDK is the layer that connects your application – and its users – to this broader, controlled ecosystem. It acts as a bridge between end users and verified business demand, enabling network participation in a way that is seamless, transparent, and aligned with modern privacy expectations.
From a developer’s perspective, the SDK is straightforward to integrate and requires minimal changes to the core product. Once implemented, it allows your app to contribute to the peer-to-business network through opted-in users, without introducing friction or disrupting the user experience.
From a user’s perspective, the process is equally simple. Participation is clearly communicated and based on explicit consent. Once a user opts in, their connection may be used to route requests to publicly available websites – without accessing personal data, interfering with device usage, or requiring any active involvement.
What makes the SDK particularly relevant in this model is how it combines passive participation with strict control mechanisms. All traffic routed through the network follows the same safeguards described earlier: verified buyers, continuous monitoring, threat protection, and compliance with international standards. The SDK doesn’t introduce new risks – it operates within an already secured and regulated environment.
At the same time, it enables a practical benefit for developers: monetization. By connecting to the network, apps can generate revenue based on active users, creating an additional income stream that doesn’t rely on ads or subscriptions. This allows developers to rethink their monetization strategy while maintaining a clean, user-friendly experience.
Frequently Asked Questions
What does “using network traffic” actually mean?
It refers to routing requests through a user’s internet connection to access publicly available websites. No personal data is accessed or collected – traffic is simply used to retrieve public information in a secure and controlled way.
Who uses network traffic in peer-to-business networks?
Only verified B2B companies use the network. These typically include businesses in e-commerce, SEO, digital marketing, market research, and cybersecurity, all of which rely on accurate, location-based access to publicly available web data.
Is my personal data exposed when participating in the network?
No, personal data is not collected, stored, or shared. The system does not access files, messages, or browsing activity. It operates strictly as a relay for public web requests, ensuring user privacy is fully preserved.
What is network traffic used for in real-world scenarios?
It’s used to access public data for tasks like price comparison, SEO analysis, brand protection, and market research. Companies rely on it to view websites as real users would, ensuring accurate and unbiased insights.
How is network traffic usage kept safe and compliant?
Safety is ensured through strict buyer verification, continuous activity monitoring, GDPR compliance, and built-in threat protection. Users participate only with consent, and all activity is governed by clear ethical and security standards.
